Despite modern, cutting-edge security technologies, cyber crime is still rampant, as attackers continue to find ways to gain unauthorized access to systems. Though the majority of software products today are built with security by design, system complexities and integrations with multiple products can introduce new verticals to the threat landscape. Zero-days—new, unknown threats—add yet another element of risk.
Even the most current vendor systems are at risk of being exploited, particularly if the company fails to take extra precautions to harden its systems and to follow best practices to maintain security across all attack surfaces. Understanding threats, taking the appropriate actions, and implementing the necessary controls give you a better chance at fending off cyber attacks, despite their unpredictable nature.
In this article, we’ll explore what you can do to address zero-day threats.
A brief overview of zero-day threats
No infrastructure is bulletproof, even if aligned with all the security hardening mechanisms. Attackers look to exploit system weaknesses, whether through known threats or via unknown threats—referred to as zero-days. Securing your systems against zero-days is challenging, as it involves finding a solution to a problem that never existed.
As such threats are discovered in the wild, they often evade existing security mechanisms, which are unable to identify them. This is why always staying up to date on security news and vendor announcements about critical patches is key. Even if it is impossible to predict zero-day attacks, practices such as implementing a mature patch management process and incident response can be helpful in reducing the risk of being exploited until a patch is released.
However, during that “waiting period,” these new vulnerabilities can be discovered by attackers looking to exploit them. Among some of the most serious serious zero-day vulnerabilities discovered have been:
- Follina MSDT: A high-severity vulnerability that performs a remote code execution. It uses the Microsoft security diagnostic tool protocol to run a malicious PowerShell code.
- Spring4Shell: Another remote code execution vulnerability, it affects applications running on Java 9 and up that use the Spring Framework.
- Log4j: This vulnerability affected a Java library used for logging, on which thousands of applications were reliant.
Why you need to be worried about zero-day threats
Traditional anti-virus software and end-point detection systems using signature-based detections usually fail to alert on zero-day threats. Instead, zero-days are usually discovered by white-hat hackers, black-hat hackers, or security-threat hunters. And even once these threats have been detected, it can take time to introduce patches or remediation steps. This time-lapse gives attackers the opportunity to exploit vulnerabilities.
Let’s take a look at how this can affect your organization.

Unknown impact
Once you become aware of a zero-day threat and know your systems could be affected, the next step is remediation. However, in the case of zero-days, it takes time until the vendor comes up with a patch, and there is not much that can be done in the meanwhile. Still, ensuring visibility into your system assets will make it easier to prioritize the assets and identify the risks. In addition, with some zero-day attacks, network protection can help.
However, the severity, impact, and exploitability of the vulnerability is only publicly disclosed later on. For this reason, as discussed above, it’s important to keep your finger on the pulse for vendor and security news updates about any vulnerabilities discovered in the wild.
Remediation can take time
Even after the zero-day vulnerability disclosure and the vendor releasing patches, not every company will act based on the severity of the vulnerability. Attackers often take advantage of this, looking to target organizations that do not act fast once a patch has been released. This is usually the result of immature patch management policies without clear timelines.
Insufficient manpower or processes to resolve
Following a zero-day vulnerability disclosure, the vendor will eventually release a patch. But not every company will be quick to apply the patch. Whether your organization relies on in-house or outsourced IT to maintain systems, a lack of resources can still be an issue when it comes to working with cross-functional teams to remediate a threat. This can increase the time from zero-day patch release till the organization implements patch management. A lack of visibility into systems and poor incident handling can also delay the process.
Prioritization Issues
There is no way of knowing when threat actors will come up with a zero-day threat, thus even multiple zero-days may be discovered within a short period of time. Companies must, therefore, analyze each threat and prioritize them based on severity and business impact.
Prioritizing critical assets can be challenging, especially for companies with a large number of assets with different asset values. Being able to identify your most critical and valuable assets is therefore key in order to prioritize them and implement patching and remediation, which will help minimize attacks on critical assets throughout the patching process.
What you can do to prepare for zero-day threats
While zero-days are unpredictable, there are still measures you can take to be prepared. These include:
- Asset identification and prioritization: Knowing which assets within the organization have been affected and prioritizing critical assets are key. Lack of visibility and improper asset identification could lead to failure to implement a patch or to remediate critical vulnerabilities in a timely manner.
- Defining the remediation timeframe: Organizations must have processes in place outlining how soon they need to fix new vulnerabilities based on severity and business impact. Failure to address critical or severe vulnerabilities can have serious consequences.
- Tracking fixes and collaboration: Poor cross-team collaboration can lead to delays in remediation, even in organizations with mature patch management policies.
The bottom line
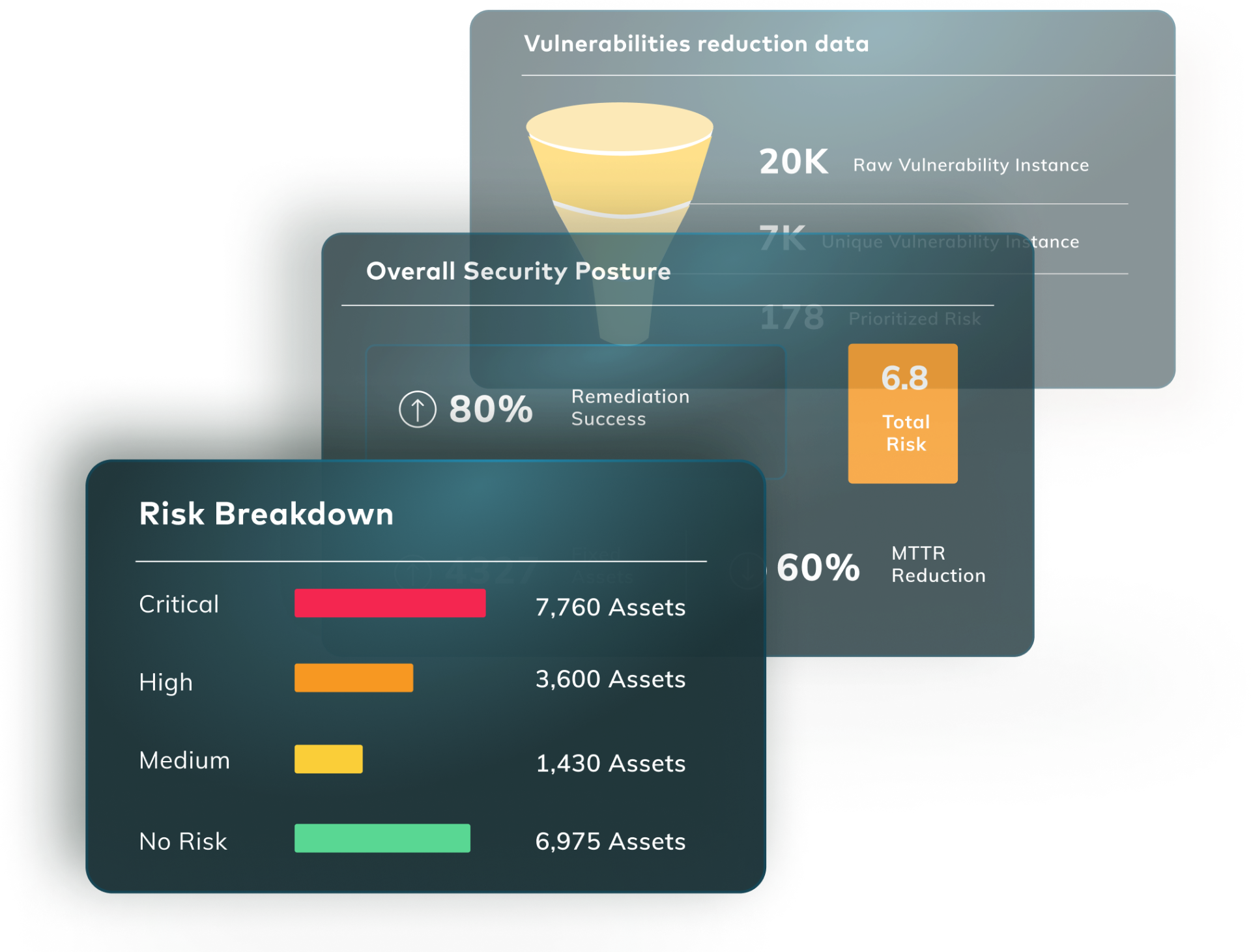
Though remediating zero-days requires waiting for the vendor to release a patch, improving your security posture and following best practices for cyber risk management can go a long way in protecting your organization. This includes asset management; prioritization of vulnerabilities not only based on severity but actual business risk; tracking, analyzing, and optimizing risk management processes; and using automation to simplify workflows and ensure accuracy.
Keep on top of emerging vulnerabilities and manage vulnerabilities at scale. Vulcan Cyber® streamlines cyber risk management through powerful remediation intelligence, vulnerability data correlation, and powerful collaboration functions so you can protect what matters most. Get your free trial, and start owning your risk today.
FAQs
Why is it called a zero-day threat?
A zero-day threat is a type of computer security vulnerability that is unknown to the party responsible for patching or otherwise mitigating the vulnerability. The term “zero-day” refers to the fact that the party responsible has zero days to prepare for or defend against an attack exploiting the vulnerability.
What are some famous zero-day attacks?
Stuxnet (2006), the Sony Pictures Entertainment assault (2014), and the SolarWinds attack in December 2020 are all instances of zero-day attacks. Zero-day attacks can steal data, destroy files, gain control of devices, and install malware or spyware.
What’s the difference between a zero-day exploit and a zero-day vulnerability?
A zero-day vulnerability is a security flaw in software or hardware that is unknown to the vendor or the public and therefore has not yet been patched or fixed. In contrast, a zero-day exploit is an attack that takes advantage of a zero-day vulnerability to compromise a system or gain unauthorized access.