Data security is more relevant than ever, especially with the spike in remote work that has led to more significant hacks and data breaches. Data security is defined as the protection of classified information from unauthorized access, and examples of such practices are encryption and access restrictions.
There are five key data security services that can protect your enterprise:
Authentication
Authentication is a simple concept – it involves the verification of a user’s login credentials and is the first line of defense against unwanted data breaches. The simplest form of authentication is known as single-factor authentication (SFA) and entails a username and password. Nowadays, some businesses use two-factor authentication (2FA) by requiring supplementary authentication factors such as thumbprints or biometric signatures for greater security.
Encryption
Encryption refers to protecting sensitive information by using an algorithm to prevent unauthorized personnel from gaining access to the information even if they have it. Viewing the encrypted information requires unlocking via an encryption “key”, which should only be made available to a select group of people to ensure the highest level of protection. Encryption can be either software-based or hardware-based.
Tokenization
Similar to encryption, tokenization replaces classified data with random characters and uses a database, known as a token vault, to store the real data. There is no algorithm or “key” involved and the only way to retrieve the real data is to submit the token to the vault.
Data Masking
Data masking is a process that changes the values of your classified data by using proxy characters that cannot be deciphered or reverse engineered without a designated software.
Physical Access Controls
While the above services represent digital access control, physical access control is also another way to ensure your data is protected. Physical access controls involve the protection of physical locations where the data resides, such as server rooms and personal workspaces. This can be done via security cameras and locks.
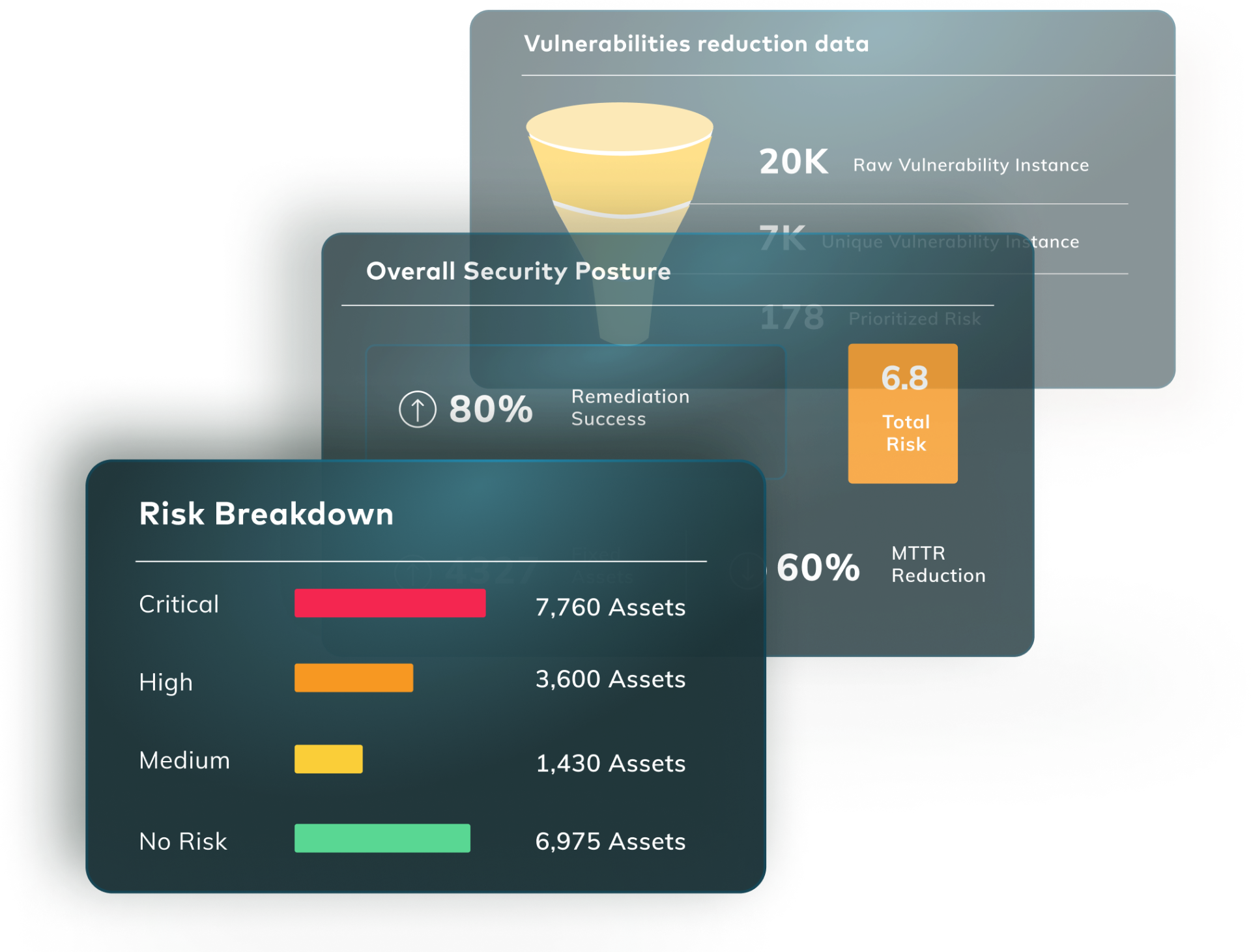
In the event that data security services fail or become vulnerable, Vulcan can help. The Vulcan platform is easily integrable and scalable to provide a swift and effective remediation, be it a patch, configuration script, workaround, compensating control or mitigating action.