Enterprises are continually exposed to security risks as the digital landscape evolves and as attackers capitalize on security gaps. Security risks need to be consistently reevaluated through regular risk assessments in order to keep your enterprise and data secure.
Following a developed Enterprise Security Risk Management (ESRM) framework will prove effective in managing risks for your business and will be much quicker once it becomes a routine. Training all staff in ESRM is vital to create a shared understanding and to mitigate avoidable risks across the organization.
Here is a simple timeline to follow during your next ESRM:
- Identify and Quantify the Enterprise’s Assets.
- It is important to identify assets and the proper stakeholder(s)/department(s) responsible for each asset in order to value them accurately
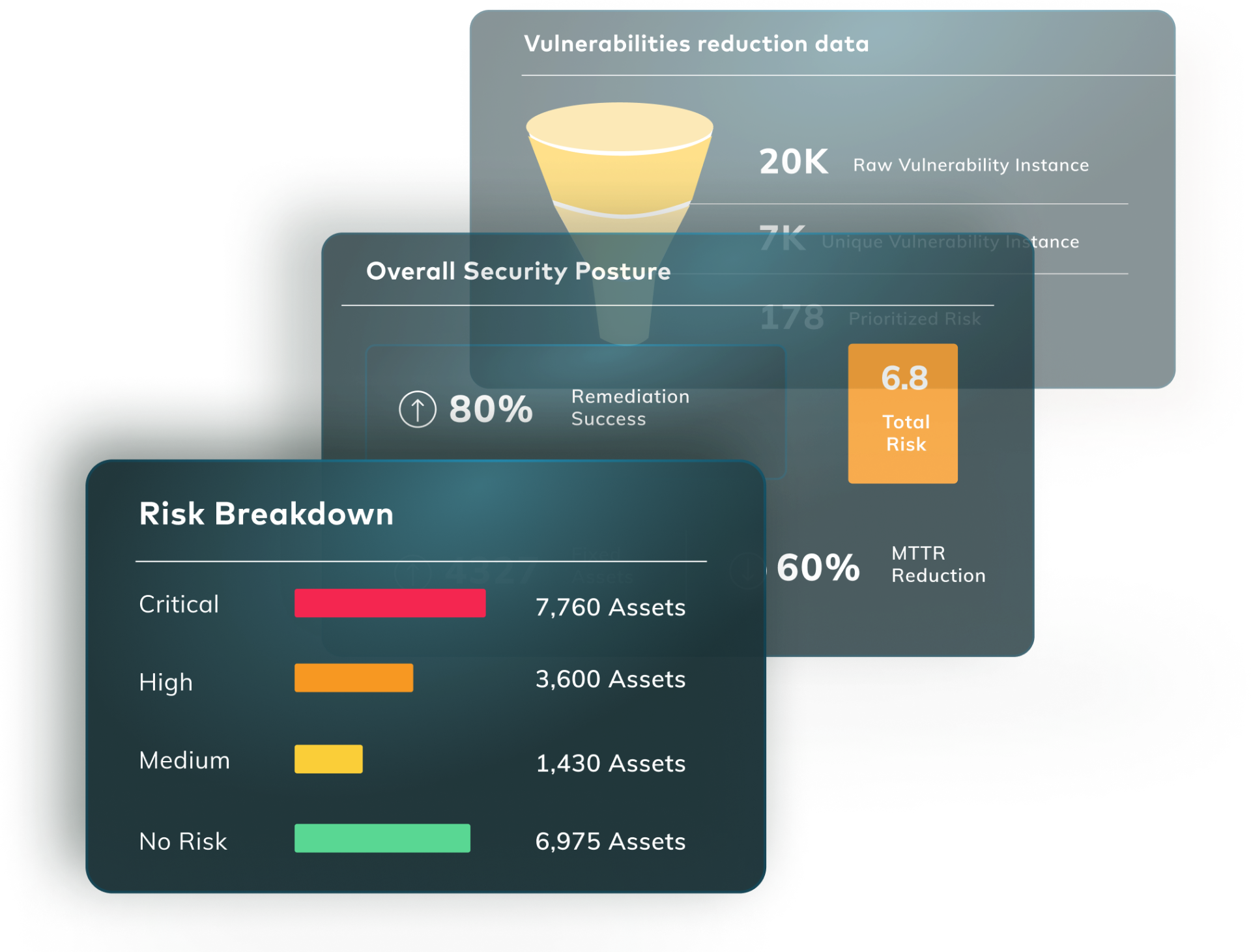
- Identify and Quantify Vulnerabilities.
- Assess the intentional or unintentional exploitation of each vulnerability, the effect on each asset, and the potentially disruptive effect on the business and its goals if a vulnerability were to be exploited
- Prioritize Vulnerabilities based on Risk
- Evaluate vulnerabilities based on severity
- This helps prioritize the resources required to address vulnerabilities
- Develop Risk Treatment Plans.
- Terminate/Mitigate/Transfer the risk.
- Identify and develop remediation plans
- Remediate.
- Implement remediation plans to remove the vulnerability
- Track and optimize based on data.
- Evaluate vulnerabilities and the respective remediation practices with past data to detect any patterns or changes that may inform future practices
- Improve.
- Consistently carry out risk assessments to measure the effectiveness of current practices and update accordingly
Full risk-based remediation can be carried out quickly with the Vulcan platform. From prioritization to remediation, Vulcan has the tools that can be scaled to your enterprise easily and effectively.