As technology continues to advance at a rapid pace, it’s not uncommon for products to reach their end of life (EoL) and be phased out in favor of newer, more advanced models. However, just because a product is no longer being actively developed or supported by a vendor doesn’t mean that it’s no longer in use. And it sure doesn’t mean its risk is going anywhere.
Here’s everything you need to know about Cisco’s new warnings for the unpatched vulnerabilities CVE-2023-20025 and CVE-2023-20026 in EoL business routers.
Why it matters?
End-of-life (EoL) products can pose a significant cyber risk to organizations. These products have reached the end of their support lifecycle, which means that the vendor is no longer providing software updates or security patches. One of the main reasons EoL products are so risky is that they often contain sensitive data. For example, an EoL router may still be connected to an organization’s network, providing access to confidential information. If a cybercriminal can exploit a vulnerability in the router — they could potentially gain access to this sensitive data.
Cisco’s new warning of critical vulnerabilities
Cisco has announced two security vulnerabilities affecting EoL Small Business routers (RV016, RV042, RV042G, and RV082). In September 2022, we witnessed the same issue with additional routers. According to International Data Corporation (IDC), Cisco holds a sizable 38.7% of the ethernet switch and router market, so you can only guess the huge impact of such an announcement.
The two vulnerabilities are tracked as CVE-2023-20025 and CVE-2023-20026, but the most severe of the two is CVE-2023-20025 (CVSS score: 9.0). In this blog post, we will be focusing on this specific vulnerability.
What is the CVE-2023-20025 vulnerability?
CVE-2023-20025 flaw is rooted in the router’s web-based management interface. This allows a remote attacker to bypass authentication or run harmful commands on the operating system. It is caused by insufficient validation of user input within incoming HTTP packets.
An attacker could take advantage of this vulnerability remotely by sending a custom-made HTTP request to the web-based management interface of susceptible routers to bypass authentication and gain elevated permissions.
Has CVE-2023-20025 been actively exploited in the wild?
The vulnerability has a public exploit code affecting multiple end-of-life (EoL) VPN routers.
Despite flagging it as a critical vulnerability, Cisco’s Product Security Incident Response Team (PSIRT) didn’t find evidence in the meantime to suggest that the vulnerability is being exploited in attacks.
Fixing CVE-2023-20025
According to Cisco: “Small Business RV016, RV042, RV042G, and RV082 Routers have entered the end-of-life process. Cisco has not released and will not release software updates to address the vulnerabilities.”
So what exactly does this mean?
- This can create a serious security risk
- Upgrading to newer and supported products is the best way to ensure security, but since it’s not possible, mitigation steps should be taken to reduce the risk
- The current recommendation is to disable ‘remote management’ and block access to ports 443 and 60443
- Go to the web-based management interface of each device > Firewall > General > disable ‘Remote Management’.
- Read the Ciscos’ security advisory to learn how to block access to ports 443 and 60443.
Next steps
Each new vulnerability is a reminder of where we stand, and what we need to do better. Check out the following resources to help you maintain cyber hygiene and stay ahead of the threat actors:
- Cyber risk in 2022- a 360° view report
- How to fix CVE-2022-3875
- Exploit maturity: an introduction
- How to properly tackle zero-day threats
- Threat intelligence frameworks in 2022
And finally…
In conclusion, organizations must stay informed about vulnerabilities and patches for all their products, including EoL ones, as they can still be used by attackers to infiltrate the network.
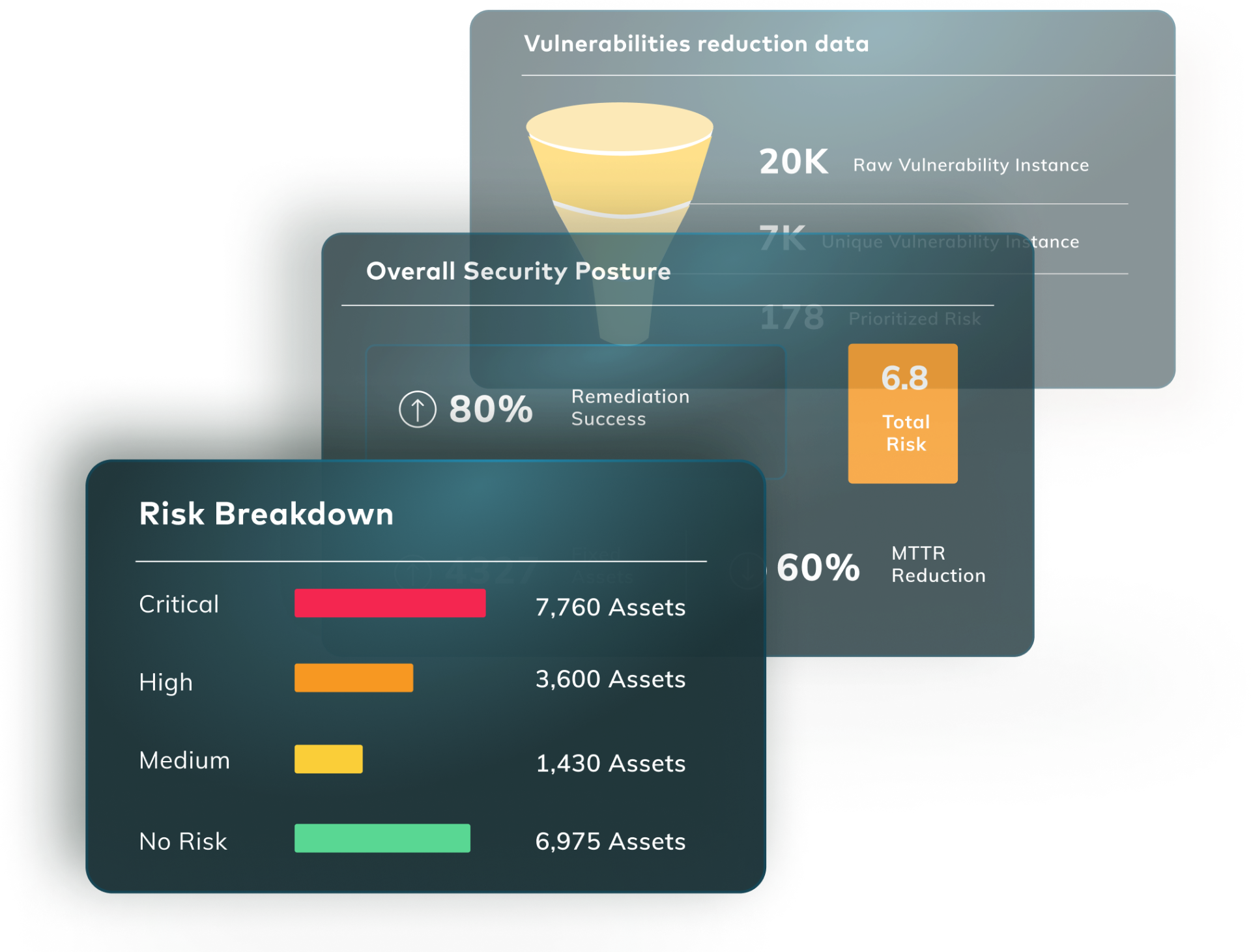
Don’t get found out by new vulnerabilities. Vulcan Cyber gives you full visibility and oversight of your threat environment and lets you prioritize, remediate and communicate your cyber risk across your entire organization. Get a demo today.