Dubbed CVE-2022-3656, The Imperva Red Team has recently discovered and disclosed a new vulnerability affecting more than 2.5 billion Google Chrome and Chromium-based browsers users. The vulnerability allows the theft of sensitive files such as cloud provider credentials or crypto wallets.
This blog will explain and demonstrate the potential impact of the “symbolic link” issue following this Chrome and Chromium-based browser vulnerability.
What is the CVE-2022-3656 vulnerability?
Insufficient data validation in File System in Google Chrome prior to 107.0.5304.62 allowed a remote attacker to bypass file system restrictions via a crafted HTML page. The Chromium security severity was tagged Medium.
This specific vulnerability was discovered amid reviewing the interactions between the browser and the different file system, and more specifically by taking a close look into the way Chromium-based browsers handle file systems. The Imperva researchers ware specifically interested in looking for common vulnerabilities that relate to the way browsers process symlinks, a type of file that points to another file or another directory.
Also known as a symbolic link, symlinks help improve performance by allowing to organize files in a more flexible way, create various shortcuts or redirect file paths. Symlinks allow the OS to treat linked files or directories as if they were placed in the same location as the symlink.
But, if not handled properly, symlinks might also include vulnerabilities. In this case for example, the root cause of the issue was in the way the browser interacts with symlinks, while processing files and/ or directories. The Imperva researchers noticed that the browser didn’t perform a proper verification of whether the symlink points to a location that was meant to have access or not. Accordingly, this allowed a “symbolic link” issue – the theft of sensitive files by gaining access to their location.

While checking the APIs that developers often use for file uploads (such as the Drop Event, File System Access API and File Input) the Imperva researchers discovered that symbolic links are usually not dealt with. Although file uploads typically have built-in safety measures, the research revealed that when dropping a file or folder onto a file input, the way it’s handled is different. Symbolic links don’t have an additional warning or confirmation for the user, they are simply processed and resolved recursively, making it possible for an attacker to take advantage of this. The attacker could create a fake website that offers a new crypto wallet service. This website could then trick and cause the user to create a new crypto wallet by requesting him to download his ‘recovery’ keys (in order to access their accounts users are required to download “recovery” keys by various crypto wallets and other online services, making it common for users to download these keys and then upload them back to the website). The keys would essentially be a zip file that contains a symlink to sensitive files or folders on the user’s computer, possibly even his cloud provider credentials. When unzipping and uploading the recovery keys back onto the website, the user would trigger the symlink to be processed, allowing the attacker to gain access to the now accessible sensitive data (files or folders). In addition, the website could be specifically crafted to appear legitimate and the process of downloading and uploading these ‘recovery’ keys could appear normal to the user, making it very probable for him not to even notice anything being amiss.
Does it affect me?
A browser’s popularity, such as Chromium’s, significantly increases the likelihood of dealing with cross-browser vulnerabilities. With a market share of over 65%, Chrome is the most widely and commonly used browser in the world. Other top browsers such as Edge and Opera are Chromium based, the open-source version of Chrome, placing Chromium’s market share at an impressive sum of more than 70% approximately.
SymStealer is the latest Chrome vulnerability discovered in recent months but it is definitely not the only one. Tracked as CVE-2022-4135, last September Google has patched a zero-day vulnerability that might potentially enable attackers to remotely execute code on a victim’s machine and cause the corruption of data and. The prior month, developer Jeff Johnson found a flaw that would allow web pages to replace the content of the system clipboard without the user’s consent or interaction.
Has CVE-2022-3656 been actively exploited in the wild?
The Imperva Red Team created a proof-of-concept (POC) attack that used CSS to manipulate the file input element in the Chromium-based browsers. By enlarging the file input element, they were able to ensure that files dropped onto the page would be uploaded, regardless of where they were dropped. This allowed the exploit of the symbolic link following vulnerability and enabled the team to steal files directly from the user’s file system.
For more details take a better look at the POC for “SymStealer” vulnerability from the original bug report on the Chromium bug tracker, the full source code also available there.
Fixing CVE-2022-3656
In order to protect crypto assets, it is important that you keep your software up to date to ensure that both your personal and financial information remains safe. Also, you should avoid clicking on links (and downloading files) from untrusted sources. Additionally, it is recommended that you use a hardware wallet to store your cryptocurrencies, a method that makes your crypto files much less vulnerable to hacking attempts as hardware wallets are not connected to the internet. Finally, consider using an efficient password manager to generate unique, strong passwords for your crypto accounts and enable a two-factor authentication process when and wherever possible.
The first fix following the disclosure of the vulnerability to Google (introduced in Chrome 107) was found not to fully address the issue, and the issue was fully resolved in Chrome 108.
Next steps
Each new vulnerability is a reminder of where we stand, and what we need to do better. Check out the following resources to help you maintain cyber hygiene and stay ahead of the threat actors:
- Cyber risk in 2022- a 360° view report
- OWASP Top 10 vulnerabilities 2022: what we learned
- How to fix the Cisco CVE-2023-20025
- How to properly tackle zero-day threats
- Threat intelligence frameworks in 2022
And finally…
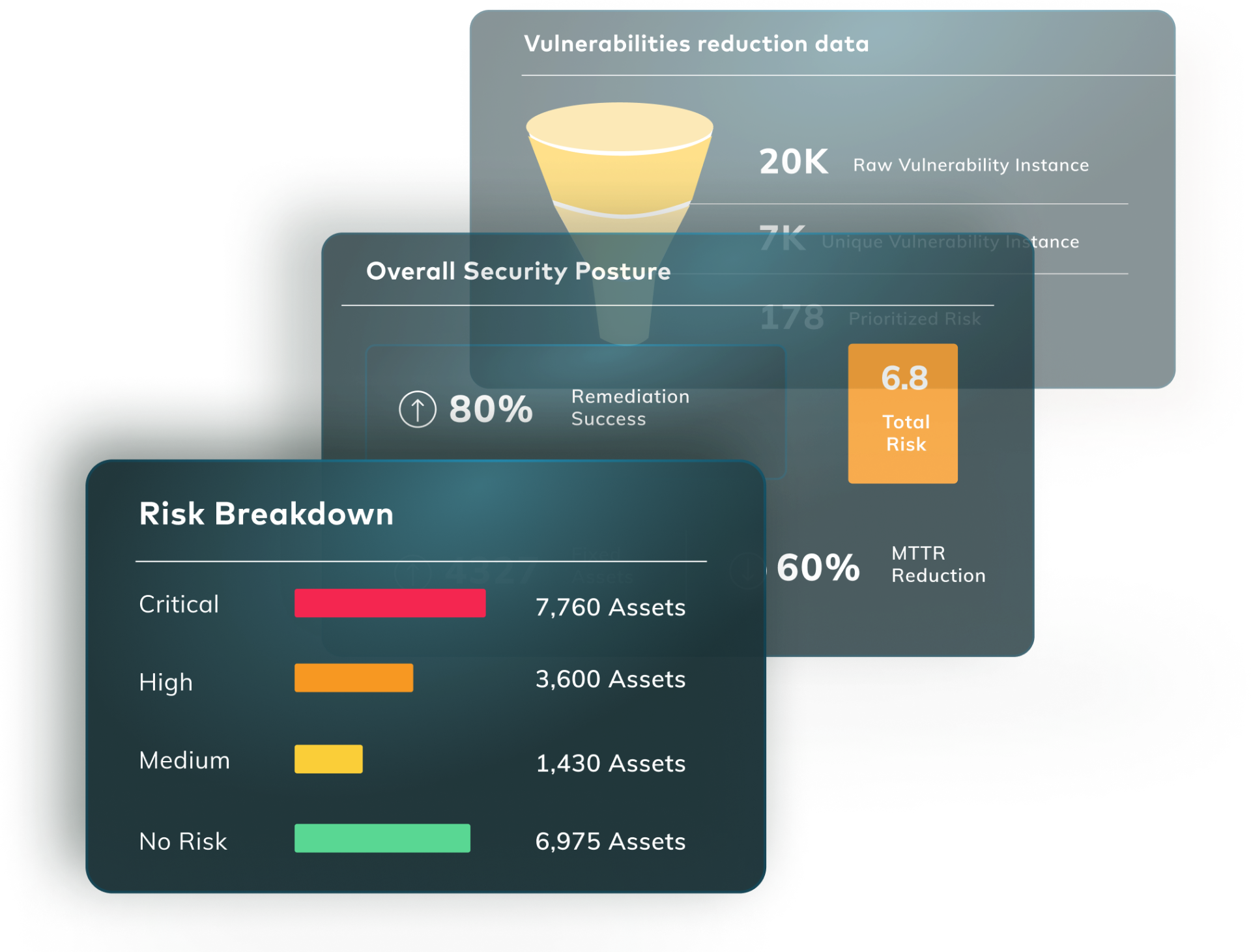
Don’t get found out by new vulnerabilities. Vulcan Cyber gives you full visibility and oversight of your threat environment and lets you prioritize, remediate and communicate your cyber risk across your entire organization. Get a demo today.