COVID-19’s widespread impacts were felt not only in everyday life but also at the workplace. The pandemic caused a total shift to remote work almost instantaneously, giving businesses little time to adapt their security plans as they moved to adopt cloud-based technologies and collaboration sites. It’s no surprise that a remote work environment results in new and more frequent threats. Here are some specifics that can help with your enterprise’s Information Security Risk Management in an online environment:
Phishing
- Phishing attacks continue to be a problem and pose heightened risks now that remote work is the norm.
- Attackers have taken advantage of the adoption of online collaboration platforms such as Slack and Zoom, often carrying out phishing attacks through those platforms instead of via email tactics which employees are more aware of.
Poor password & VPN security
- With remote work driving the use of virtual private networks (VPNs) and remote desktop protocol (RDP), attackers have taken advantage of this to exploit poor password security and VPN vulnerabilities to access classified data and plant malware.
Vulnerable and Compromised Endpoints
- Working remotely means working outside corporate parameters. Without the heightened security from cyber defenses within the corporate parameters, employees are more vulnerable to cyber attacks.
- Employees working on personal devices are also more susceptible to attacks since they are less likely to be compliant with corporate security policies.
The increased use of cloud-based technologies has resulted in a greater attack surface that is harder to protect.
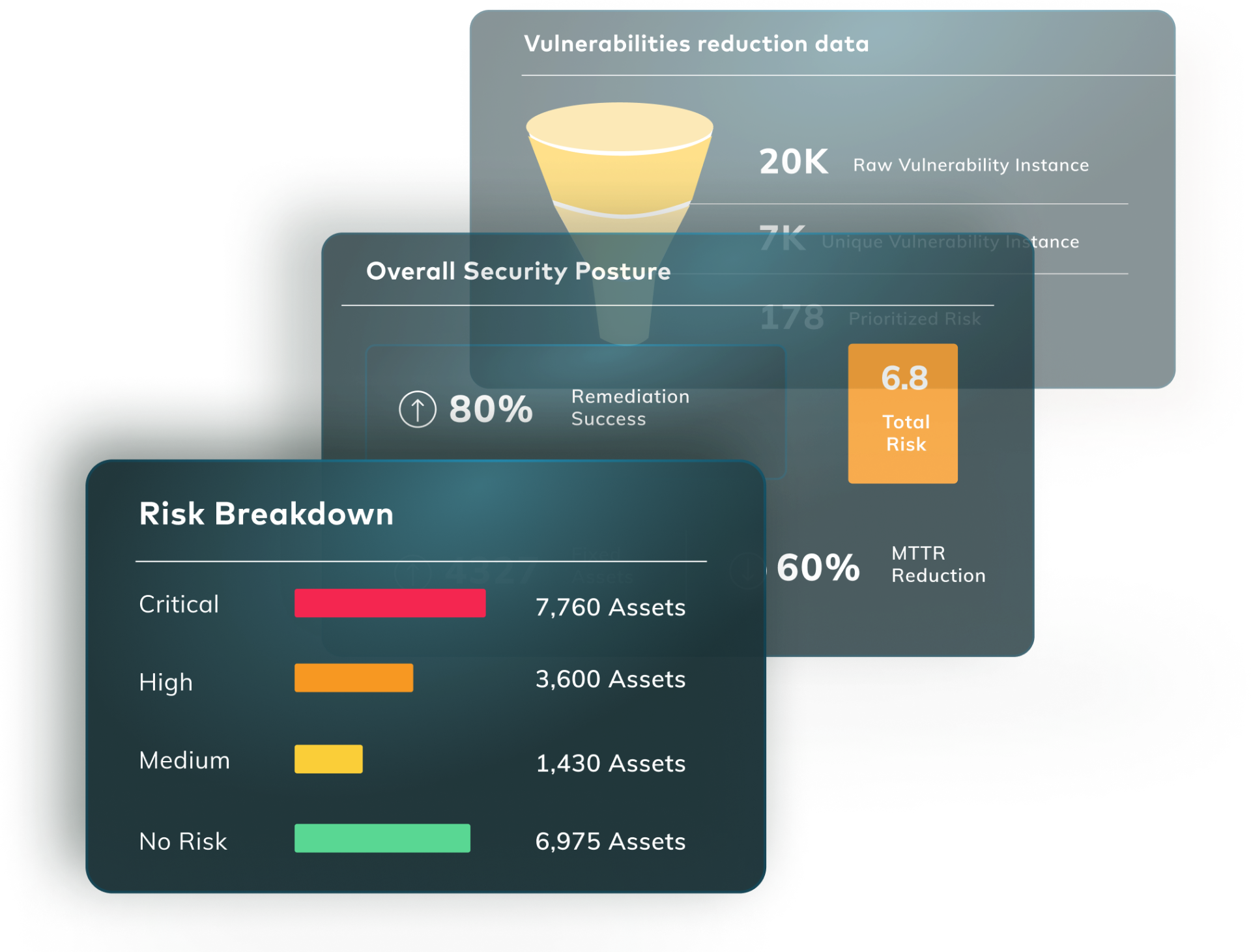
Vulcan provides a functional risk-based remediation platform that can help. Vulcan has streamlined the entire process to make cybersecurity easily attainable and scalable for your business, from prioritizing to getting fix done.