As the world’s largest software vendor, it probably stands to reason that critical Windows vulnerabilities appear more often than others. Even though Microsoft is typically very fast to release patches—either on Patch Tuesday, the second Tuesday of every month, or as an out-of-band release in an emergency—getting those patches implemented across your entire organization isn’t always easy. For example, even though Microsoft released a patch in July 2021 for the Windows Print Spooler Remote Code Execution Vulnerability, in March 2022, CISA warned that Russian state-sponsored cyberattack groups were continuing to exploit this vulnerability.
Staying aware of today’s top threats and their remediation steps is essential in order to avoid falling victim to sophisticated and well-funded attackers.
As a service to the community, Vulcan Cyber® offers Remedy Cloud, the world’s largest resource of expert-curated vulnerability solutions to help you navigate the constantly changing security landscape. And, according to Remedy Cloud, here are the top Windows vulnerabilities, and how to fix them:
Windows Print Spooler remote code execution CVE-2021-34527
- Nickname: PrintNightmare
- Product: Microsoft Windows
- Threat: Remote code execution
- Patched: July 1, 2021
The print spooler is exactly what it sounds like—a small component included with every copy of Windows that controls print queues. Because it’s part of every single Windows installation, it’s essentially ubiquitous—low-hanging fruit that attackers can exploit to gain system-level privileges and run arbitrary code.
Exploitation of the print spooler vulnerability was detected in the wild relatively early, and it seems reasonable to assume that attackers will continue to exploit this vulnerability given the vast numbers of systems that have still not been updated. For those and other reasons, this vulnerability made almost every security organization’s Top 10 list for 2021—and it may also make the list for 2022, given that it’s still being exploited.
Systems affected by CVE-2021-34527 include nearly all versions of Windows. Check the full list and follow all steps outlined here. It is likely that unsupported versions of Windows also contain this vulnerability, in which case, if a system upgrade is impossible—due to legacy hardware or software—then the print spooler service should be disabled.
Exchange ProxyLogon CVE-2021-26855
- Nickname: ProxyLogon
- Product: Microsoft Exchange Server
- Threat: Server-side request forgery (SSRF), authentication bypass
- Patched: March 2, 2021
A number of vulnerabilities have come to light recently targeting on-premises Microsoft Exchange Servers, enabling attackers to access email accounts as well as providing a vector through which to introduce additional malware. Further vulnerabilities in the Microsoft Exchange Server led to the development—after ProxyLogon was patched—of a similar vulnerability generally known as ProxyShell (CVE-2021-34473).
ProxyLogon originally emerged as a zero day, with attacks taking place in the wild as early as January 2021. This and other Exchange Server vulnerabilities have been a critical attack vector for HAFNIUM, a state-sponsored advanced persistent threat (APT) group operating out of China. ProxyLogon and ProxyShell also made many of the “most frequently exploited” lists of 2021.
Systems affected by CVE-2021-26855 include Windows Server 2004, 2008, 2012, 2016, 20H2, and 2022. Be sure to check the full list at Microsoft’s Security Response Center and download all relevant updates (Since updates are cumulative, the most recent update will include this patch.).
Elevation of Privilege Vulnerabilities CVE-2021-42278 and CVE-2021-42287
- Nickname: noPac
- Product: Windows Server
- Threat: Privilege escalation
- Patched: November 9, 2021
These are both vulnerabilities in Microsoft domain controllers, with CVE-2021-42287 affecting Active Directory Domain Services (AD DS) and CVE-2021-42278 affecting Security Account Manager (SAM). When the two are combined, they take on what security pros are calling a “weaponized” form, letting an attacker escalate privileges and take administrator-level control of the compromised system.
Potential consequences include shutting down or manipulating a domain or site, leaking private and protected information for ransom or sale on the dark web.
What IT pros probably find most horrifying about noPac is how easy it is to exploit. According to proofs of concept that began being widely circulated in December 2021, it only takes a knowledgeable attacker around 16 seconds to grant domain admin authorization to compromise a domain. And although a patch is available, as long as a single unpatched domain controller server remains, the entire environment continues to be vulnerable.
Systems affected by CVE-2021-42278 and CVE-2021-42287 include Windows Server 2004, 2008, 2012, 2016, and 20H2. Please check the full list at Microsoft’s Security Response Center and download all relevant updates (since updates are cumulative, the most recent update will include this patch).
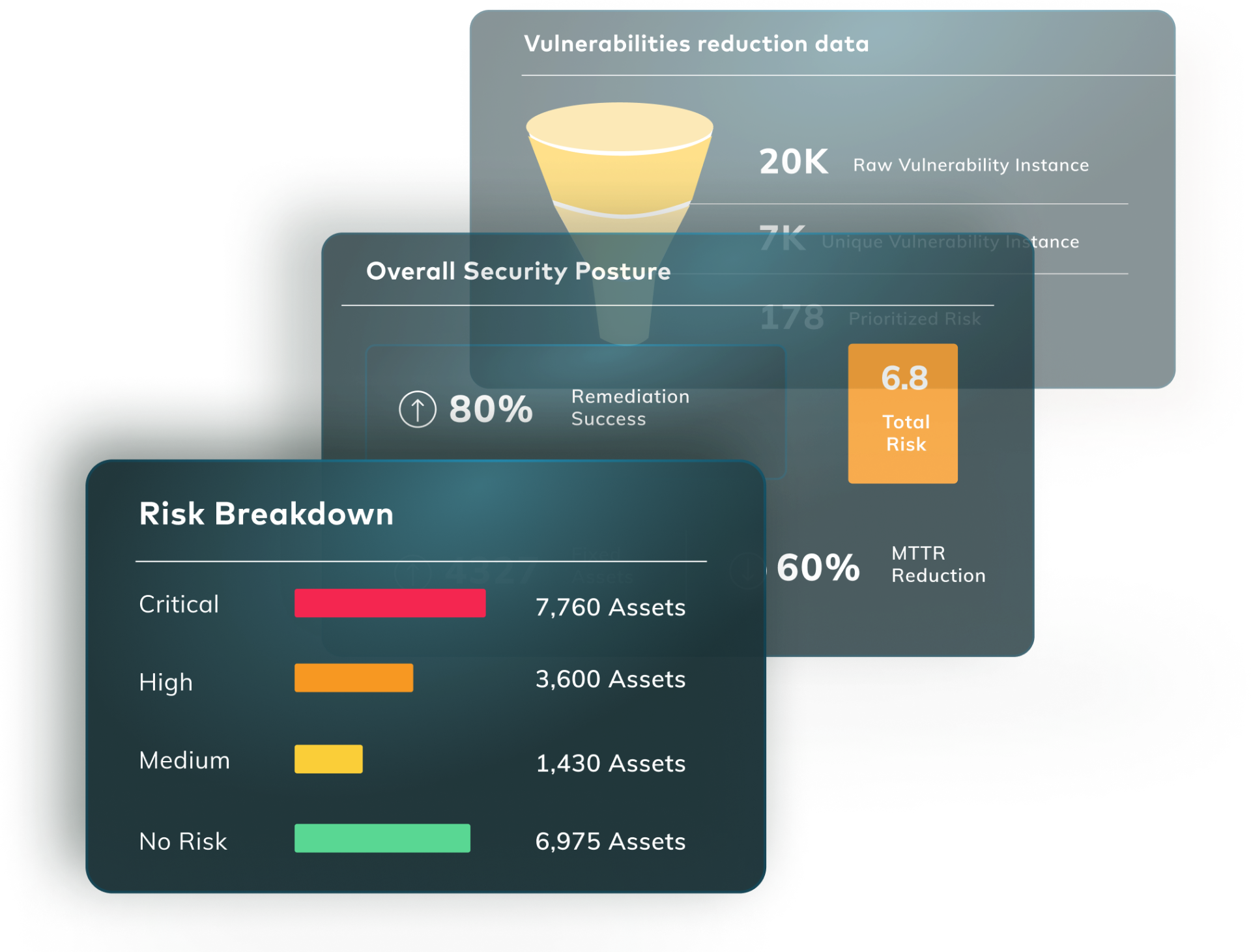
Fix Printnightmare and other Windows vulnerabilities
The Vulcan Remedy Cloud is the world’s largest vulnerability database dedicated exclusively to remediation to give you quick access to the fixes you need, matching your prioritized Windows vulnerabilities with the right remedies to own your risk.