A simple definition for vulnerability remediation is the process of finding the security weak spots in your digital infrastructure, then applying remedies to the most-critical issues as quickly as possible to reduce cyber risk. In practice though, vulnerability remediation is far from straightforward. Remediation to reduce cyber risk isn’t possible without the help of IT and engineering teams who are often stuck with a crushing work load to get fix done.
This post explores the growing challenges of vulnerability remediation. It pinpoints the true vulnerability management endgame of detecting each vulnerability and applying the right fix as fast as possible, while verifying the vulnerability has been resolved.
We’ll also cover vulnerability remediation best practices, common traps to avoid, and the importance of automation. Finally, we discuss the Vulcan Cyber platform and its approach to deliver remediation orchestration by helping security and IT teams prioritize, remedy, automate, and analyze cyber risk and the vulnerabilities that cause it.
The Struggle to Reduce Cyber Risk Through Vulnerability Remediation
In the early days of vulnerability management, when the first vulnerability scanners were introduced to cyber security teams decades ago, vulnerabilities were far and few compared to today. Each team could handle its own. But threats to network security have grown dramatically with the technological changes and advances we’ve seen.
Thanks to the cloud and changes to enterprise infrastructure, networks have become more exposed to external threats. Public cloud, open-source software, and third-party solutions have added to that exposure. Meanwhile, real-time visibility into vulnerabilities has shrunk at the same rate.
Today, complex, multi-cloud, hybrid architectures and diverse stacks comprise multiple solutions and vendors increasing cyber risk. This adds another layer to the problem. With the massive shift to agile development and rapid code releases software is often deployed without adequate testing or security checks.
Vulnerability Management vs. Vulnerability Remediation
Simply put, vulnerability remediation is the desired outcome of any vulnerability management initiative, but is too often never realized and cyber risk isn’t mitigated. But why is this?
Vulnerability management focuses on these areas:
- Knowledge: Knowing the latest security threats. This is often done through information automatically collected from security product vendors, system updates, and threat intelligence reports.
- Discovery and visibility: Knowing how your systems’ components interact, how many instances you have of various software components, where the access points to your network are, who “owns” what, etc.
- Assessment: Scheduling frequent assessment scans to detect new vulnerabilities.
- Prioritization: Determining which vulnerabilities pose the greatest cyber risk to your specific network and prioritizing those vulnerabilities for remediation.
Effective vulnerability remediation focuses on preempting threats before they can do any harm. Ideally, this includes multiple teams from management and developers, to IT and security working across departments to improve cyber hygiene, reduce cyber risk through the most efficient methods possible.
Automation should be used whenever possible, not only to save time and money by working at scale, but to ensure consistency.
Getting Started with Vulnerability Remediation
Every company is unique, but we recommend all vulnerability remediation programs contain these elements:
- Increase awareness of vulnerabilities: Communicate the importance of vulnerability remediation with the C-suite, IT, security, and DevOps teams. Identify how they can contribute to the efforts.
- Guard your CI/CD pipeline: New technologies require new remediation strategies. With more vulnerabilities being pushed into production than ever, measures need to be taken to protect the CI/CD pipeline.
- Maintain a complete inventory of your network’s assets: Assessing the threats posed by vulnerabilities in your network can only be done accurately if you have complete visibility of your network, know which assets are connected, and how they interact.
- Know which vulnerabilities to prioritize: While CVSS can offer “objective” severity ratings, your team needs to prioritize vulnerabilities based on how they impact your specific environment. Vulnerabilities have an element of subjectivity to them, since exploiting the same vulnerability has a different impact on different environments.
- Think twice before you patch: Applying a patch is often the best way to remediate a vulnerability. But patches introduce their own type of cyber risk to an IT environment and might break production infrastructure, especially with how interconnected information technology is these days. Sometimes a configuration change or a workaround is all you need to safeguard your network. Vulcan Cyber developed its proprietary remediation intelligence database—including Remedy Cloud, its free, community version—to inform security teams about the most efficient solution to any threat. That might be a patch, configuration change, mitigating action, compensating control or workaround. Understanding your options allows for the least disruptive solution to be implemented.
- Orchestrate and analyze: With so many moving parts, the remediation effort needs to be orchestrated to be successful. And you can’t fix what you can’t measure. Continuous orchestration and analysis is necessary for remediation at scale.
- Re-scan: Scan and validate that the threat has been completely removed from the system.
These steps are more efficient if your company uses a vulnerability mediation intelligence database and vulnerability threat intelligence. With these tools and processes in place, you can be sure you have the latest remedies and the ability to drive remediation outcomes.
Benefits of Automation
Aim to automate as much work as you can when implementing your vulnerability remediation program. Automation saves time, improves quality of remediation, and drives consistency. For many companies, automation is the only practical way to implement remediation due to the size and complexity of the networks and components involved.
- Automation reduces manual errors: Keep your team’s focus and energy where they can add more value, while avoiding the errors associated with manual, repetitive, mundane tasks.
- Automation reduces vulnerabilities in your CI/CD pipeline: Application security scanners keep an ever-vigilant eye on your pipeline, reducing risk of deploying compromised code.
- Curated remediation intelligence saves time and effort: Retrieve information automatically from vendors, forums, and other sources, instead of having your team search for it. Use Remedy Cloud and avoid doing this dirty job yourself.
- Vulnerability prioritization: Automating the prioritization of threats to your network will help focus on remediation of the most impactful vulnerabilities.
- Solutions are applied consistently: In networks with multiple instances of the same component, configuration automation guarantees the same remediation method is applied to each.
- Solutions are applied continuously: Automation makes it possible to remediate using automated scripts and playbooks to apply solutions continuously.
- Solutions are applied in the correct order: An automated script can apply multiple solutions to one or a group of components, in the correct order.
- Enterprise-grade scalability: Automation allows for efficient remediation at scale.
Vulnerability Traps and How to Avoid Them
Avoid these expensive vulnerability mediation traps that only waste time and increase cyber risk:
Trying to Patch Everything
The vast number of vulnerabilities (tens of thousands) detected each year make it impossible to remediate everything. Besides, patching can be risky so it should be reserved for the cases where it’s the most appropriate course of action.
Focusing on the Wrong Threats
Vulnerabilities with a low CVSS rating might have active exploits, while other “critical” vulnerabilities might not directly concern your environment. In other words, if you focus on external designations, you might be ignoring threats that pose the greatest risk to your company while wasting time on ones that are less relevant.
Believing the Hype
Media coverage often hypes up critical problems and disasters, which can exaggerate their importance. Consider the Spectre and Meltdown threats. Both were heavily promoted, but ended up having a minimal impact. Anyone swept up in the hype wasted time and money without reducing cyber risk and improving cyber hygiene.
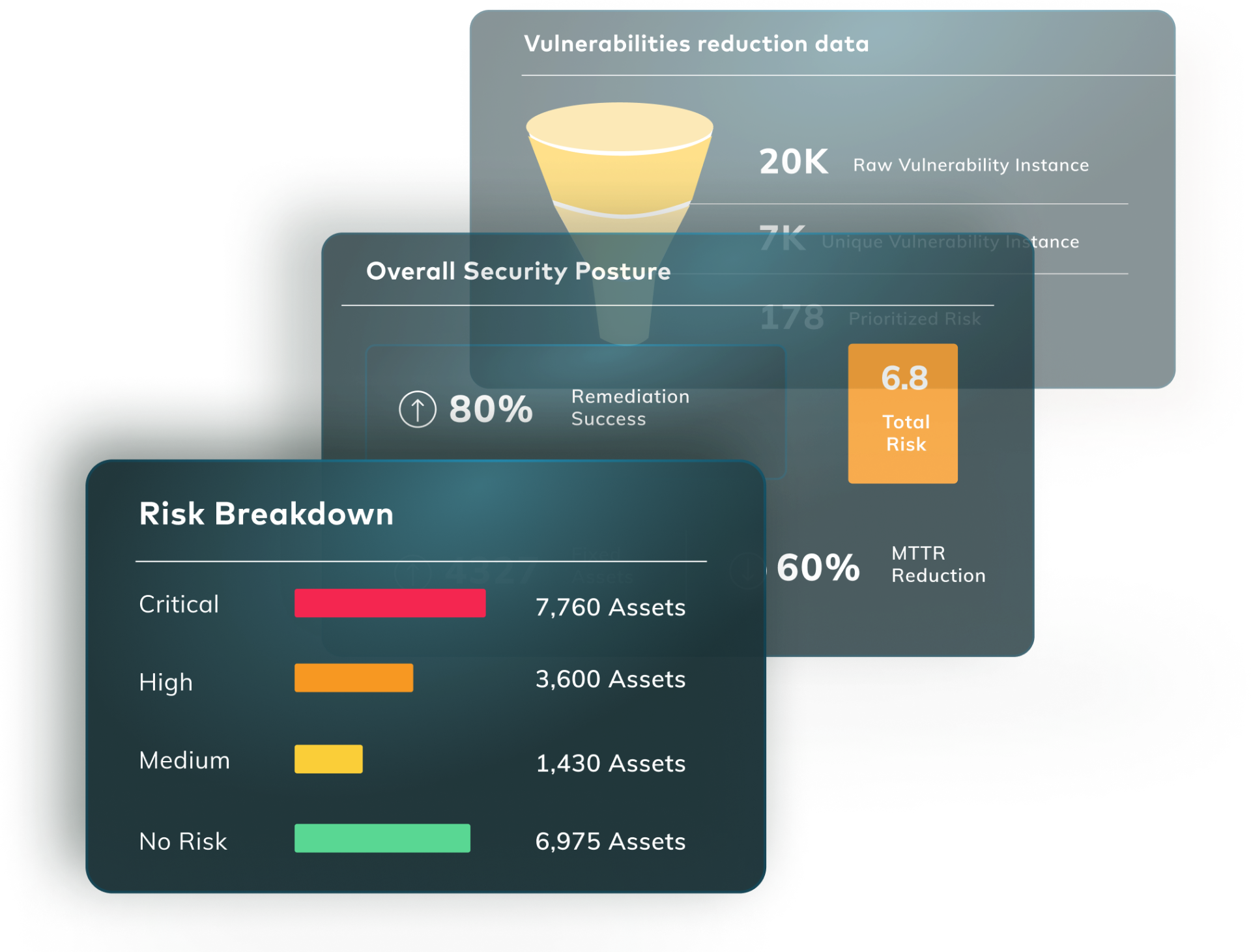
The Vulcan Cyber Approach to Vulnerability Remediation
The Vulcan Cyber remediation orchestration platform allows security teams to safeguard against vulnerabilities.
Vulcan Cyber:
- Prioritizes, pinpointing business-critical threats according to the unique risk they pose to your environment.
- Remedies, with a range of options from configuration changes to patches based on your network’s specific characteristics.
- Automates, scaling the remediation process through workflow automation and orchestration across teams.
- Analyzes, providing clear end-to-end remediation campaigns that ensure remediation outcomes are achieved, service-level agreements are met, risk is reduced, and compliance is realized.
Vulcan Cyber offers a couple of ways to experience the power of our remediation orchestration platform. First we offer Vulcan Free, which is the industry’s only vulnerability prioritization tool. Next we offer a free remediation intelligence database, known as Remedy Cloud, which provides curated solutions and fixes to thousands of vulnerabilities, giving teams the most-efficient solutions to any security threat.
The Vulcan Cyber platform orchestrates vulnerability remediation, with out-of-the-box and customizable playbooks to ensure threats are removed consistently, safely, and efficiently. Vulcan Cyber helps cyber security and IT teams realize the full potential of a well-run vulnerability management program and get fix done.
To see the Vulcan Cyber remediation orchestration platform in action schedule a demo with a member of the Vulcan Cyber team today.