Last week, we had the privilege of hosting the highly informative CyberRisk Summit, held twice a year, bringing together a diverse group of cyber risk experts from various industries and companies. Throughout the event, these experts shared their top cyber security advice, tips, and profound knowledge on a wide range of topics, delving into the realms of cyber risk and vulnerability risk management in… challenging times.
The summit provided a unique opportunity for the Vulcan Cyber community to gain valuable insights and practical strategies to tackle the ever-evolving challenges posed by cyber security threats. From discussions on risk assessment methodologies to the implementation of effective management at scale, the summit covered a broad spectrum of crucial subjects. With each session, we deepened our understanding of the complex cyber landscape and discovered innovative approaches to enhance our organization’s cyber resilience.
The valuable lessons learned and the knowledge gained during the summit will undoubtedly play a pivotal role in strengthening our cyber security posture and fortifying our defenses against potential threats in the future.
Here are the main takeaways from CRS this time around:
Session 1 – Helping enterprises mitigate cyber risk at scale
Speaker: Yaniv Bar-Dayan, Vulcan Cyber CEO
1. The enterprise attack surface is expanding
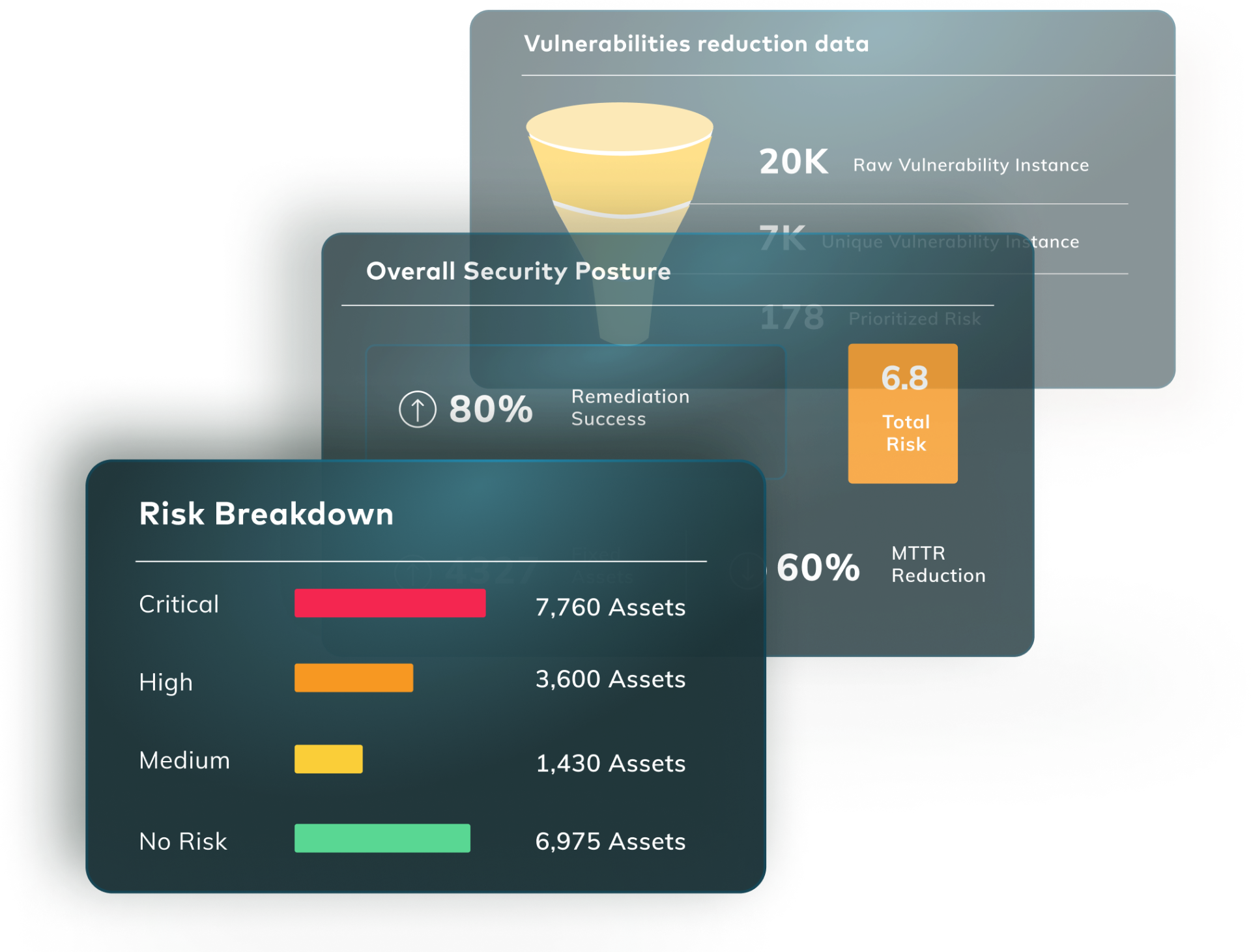
The attack surface grows as we speak, with large corporations, smaller enterprises, hyperscale tech companies, and more, relying heavily on scanning tools to identify vulnerabilities, assess risks, and gain insights into their enterprises’ attack surface and posture.
2. Vulnerability risk management is a multi-tool effort
Enterprises employ multiple tools (up to 20) to collect information for risk identification and vulnerability management. These tools produce thousands of new vulnerability instances and hundreds of thousands of critical vulnerabilities daily, sourced from infrastructures, code projects, applications, and SaaS.
3. There’s always someone in charge
The difficulty of remediation lies in identifying the right remediation owner for each finding, which requires associating ownership data distributed across different systems and databases.
4. Processes also need to scale
The ability to scale the process of managing vulnerabilities effectively is crucial for enterprises, especially as they continue to onboard new tools and face regulatory compliance requirements.
5. Follow the steps
Scaling the vulnerability management process involves steps such as correlating data, enriching findings with contextual information, prioritizing vulnerabilities, associating tasks with owners, and measuring progress.
Watch the full session here >>
Session 2 – CISO perspectives on efficient cyber security with limited resources
Speaker: Frank Kim, YL Ventures CISO in residence
1. Principles matter
When dealing with limited resources, it’s important to go back to first principles and focus on the fundamental concepts of cyber security. Often, in the midst of daily emergencies and distractions, common sense practices may be overlooked. Remind yourself and your team of the basic principles and turn them into common practice.
2. Don’t forget the goals
As a security leader, your role extends beyond implementing controls to encompass managing information risk for the organization. Understanding business objectives and aligning your security program with the broader goals of the organization are crucial aspects of this responsibility.
3. Cyber risk is business risk
Treat cyber security as an enterprise risk issue, not just an IT issue. Like other risks faced by the organization, cyber risk needs to be managed strategically. Take into account strategic, financial, operational, legal, and reputational risks, as cyber security risk cuts across all these areas.
4. The risk equation
Assess the likelihood and impact of cyber security risks. Likelihood refers to the probability of a security incident occurring, while impact refers to the potential harm or consequences of such an incident. Consider the interplay between likelihood and impact to determine the level of risk and prioritize efforts accordingly.
5. Control with compensating controls
When faced with high-risk scenarios, focus on implementing compensating controls and processes to mitigate the risk. Compensating controls are security measures or practices that can help bridge the gap and reduce the likelihood or impact of a security incident.
Watch the full session here >>
Session 3 – Prioritizing vulnerability risk at Verana Health
Speaker: Jayashree Jagannath, director of security and compliance at Verana Health
1. Get your cyber risk together
One of the challenges faced was the lack of a unified view of vulnerabilities. With different sources providing vulnerability data, it was important to get a single pane of glass for teams to effectively assess and resolve vulnerabilities.
2. Assets, not just vulnerabilities
Proper asset management was crucial for understanding what needed to be protected or monitored. Verana Health’s data and assets are highly sensitive as they are operating in the world of digital health analytics. Setting up a structured account structure and standardized tagging helped categorize and assess risks associated with different assets.
3. Vulnerability and patch management fatigue
Managing and prioritizing vulnerabilities, as well as patching them, posed a challenge due to the continuous influx of vulnerabilities. Prioritizing vulnerabilities based on risk and establishing SLAs for timely fixes helped address this issue and build urgency wherever it was needed.
4. Build a security culture
Building a culture of security was emphasized, involving educating teams, promoting a top-down approach, and integrating security practices into the development process. A shift left mentality and instilling secure coding practices were important aspects of the security culture.
5. Choosing the right platform to manage risk
Criteria for selecting a tool that will be used to manage vulnerability risk included the ability to integrate with different vulnerability sources, ease of asset classification and risk communication, vulnerability prioritization organization’s specific measures, advanced reporting and analytics, and providing sufficient information to developers for fixing vulnerabilities.
Verana Health selected Vulcan Cyber vulnerability risk management platform due to product features that addressed their challenges such as The Vulcan connectors and integration capabilities, single pane of glass for asset risk management, automated campaigns for vulnerability scanning and ticket creation, reporting and analytics functionalities, integration with Jira for tracking and resolving vulnerabilities, prioritization and remediation based on threat intelligence and business risks.
Watch the full session here >>
Session 4 – Getting the most out of EPSS and CVSS for risk prioritization
Speakers: Roy Horev, Vulcan Cyber CTO, and Octavian Suciu, postdoctoral cyber security research
1. What is EPSS?
EPSS (Exploit Prediction Scoring System) is a community-driven effort that aims to derive a probability of observing exploitation activity in the wild within the next 30 days. It is based on machine learning and collects data about vulnerabilities and exploits to predict future exploitation activity.
2. EPSS vs. CVSS
EPSS is not designed to replace CVSS (Common Vulnerability Scoring System) but rather complement it. While CVSS focuses on the characteristics of vulnerabilities, EPSS takes into account additional factors such as exploit availability, attacker skills, and patching cadence to provide a more accurate prediction of exploitation likelihood.
3. EPSS is a vulnerability prioritization factor
EPSS predictions are updated daily and should be used in conjunction with other risk management information and contextual factors. It helps prioritize resources within the high CVSS score bucket by considering vulnerabilities with high CVSS scores and high probabilities in EPSS.
4. Not everything is perfect
Feedback on EPSS has highlighted two main challenges: transparency and completeness. Users often want to understand why EPSS scores change and have more transparency into the underlying data. However, contractual obligations with data partners limit the level of transparency that can be provided. EPSS is also not a comprehensive risk assessment tool and cannot capture all environmental and compensating control factors.
5. The golden advice for infusing EPSS into day-to-day risk management
Start with threat intelligence. If vulnerabilities are already known to be high-priority through threat intelligence, focus on those first. Then, leverage EPSS by combining its probability output with contextual and environmental information from other sources to set priorities accordingly. EPSS should be seen as one tool among others in the risk management process.
Watch the full session here >>
Session 5 – Putting cyber security data to work at scale
Speakers: Yitzy Tannenbaum Vulcan Cyber director of product marketing, Annam Iyer Wiz product manager, Steve Boone Checkmarx head of product growth, Yochai Corem Cyberint CEO, Andrew Grealy CTCI CEO
1. The Vulcan Cyber integration engine
We acknowledge the importance of integrating to a wide variety of cyber security tools, fast. The new integration engine allows for seamless and speedy integration with various security tools in an organization’s ecosystem. We have over a hundred out-of-the-box connectors and also provide a low-code way to integrate with unique or custom security solutions.
2. The Vulcan Cyber Wiz integration
Wiz offers an agentless scanning approach for cloud workloads, utilizing APIs provided by different cloud service providers. They scan and analyze resources across multiple cloud environments, including AWS, Azure, GCP, Oracle, and AliCloud. Wiz has recently integrated with Vulcan Cyber, allowing customers to get a comprehensive view of cloud vulnerabilities posture and de-duplicate findings for prioritized remediation actions. This integration simplifies the process and helps customers make informed decisions about their cloud vulnerability management.
3. The Vulcan Cyber Checkmarx integration
Checkmarx offers an application security platform that includes various engines for static application security testing, software composition analysis, infrastructure as code scanning, container scanning, dynamic application security testing, and API security. Checkmarx’s integration with Vulcan enables seamless orchestration and automation of security actions. The integration allows for automated security scans and actions, saving time and effort for security teams. Real-time threat response becomes a reality, as security scans can be initiated automatically within the platform.
Watch the full session here >>
Session 6 – The establishment of a collaborative vulnerability management program
Speakers: Samira Jamnejad, WealthSimple Security Assurance Manager; Noy Sinai, Vulcan Cyber VP of Operations
1. Focus on remediation gaps
Building a vulnerability management program involves understanding and addressing gaps in the remediation process, such as ticket comprehension difficulties, risk acceptance, and the need for effective communication.
2. Follow the key steps in vulnerability management
Identification, prioritization, and remediation are crucial. Without effective remediation, identification, and prioritization efforts do not significantly reduce risk.
3. Identify risk everywhere
Utilizing different scanners, detection sources, and bug bounty programs for comprehensive vulnerability identification.
4. Provide remediation guidance
Remediation may be challenging for engineers, so providing guidance or solutions is essential for effective resolution.
5. Integrate the right tools
Using platforms like Vulcan Cyber and Jira offers a unified view of vulnerabilities, aiding in risk-based prioritization. The integration streamlines communication with engineering teams and provides insights through a dedicated vulnerability management board. Using teams’ native tools also helps with ongoing, two-way communication and fosters a healthy relationship, mutual trust, and continuous improvement in the vulnerability management program.
Watch the full session here >>
Session 7 – Agile security: How Paystack empowers Its small security team for effective cyber risk management
Speakers: Jocelyn van Heerde, Paystack Information Security Engineer; Nino Klimiashvili, Vulcan Cyber Customer Success Manager
1. Get your vulnerability management efforts together
Manage risk through a centralized hub for vulnerability management streamlines workflows, reducing manual efforts.
2. Group assets together
Leverage features like asset grouping and tagging to facilitate precise triaging based on risk prioritization and business impact.
3. Establish accountability and KPIs
Use personalized dashboards and KPIs for security measures within teams.
4. Enhance progress visibility
Build comprehensive dashboards that provide an overview of the organization’s risk posture, fostering better engagement and collaboration.
5. Explore, but reevaluate
Exploring solutions, tactics, and methods. Reevaluation is crucial as tools may evolve to meet specific needs.
Watch the full session here >>
Session 8 – The shift to exposure management
Speakers: Yaniv Bar-Dayan, Vulcan Cyber CEO & Co-founder
The rise of exposure management
In this evolving digital era, exposure management emerges as a central focus. It extends beyond traditional vulnerability management, encompassing a wider array of threats including cloud issues and misconfigurations across diverse attack surfaces.
Meeting the demands of digital transformation
With enterprises becoming increasingly digital, there’s a pressing need for robust security across all layers, from network and cloud applications to emerging technologies like IoT and SaaS. This necessitates gaining expertise in a variety of security domains.
Emerging trends in cyber security frameworks
The landscape sees the emergence of new categories such as Cyber Asset Attack Surface Management (CAASM), Unified Vulnerability Management (UVM), and Application Security Posture Management (ASPM). These represent steps towards an integrated exposure management strategy.
Future outlook: Integrating and streamlining security
Looking ahead, exposure management is set to encompass even more categories, leading to a comprehensive approach that simplifies and strengthens cyber security practices.
You can watch the full session here >>
Session 9 – Managing cyber risk and expanding attack surfaces in 2023
Speakers: Rickard Carlsson, Detectify CEO; Yaniv Bar-Dayan, Vulcan Cyber CEO & Co-founder
Tackling zero-day vulnerabilities proactively
Given the increasing prevalence of zero-day vulnerabilities, organizations should not solely rely on public CVE lists. Instead, they need to proactively seek out these vulnerabilities, which often require more advanced detection methods and tools tailored to the specific nature of zero-day threats.
Prepare for operational challenges in breach situations
Organizations must develop robust incident response strategies to handle the operational challenges and trust issues arising from cyber security breaches. This involves maintaining transparency with stakeholders and having clear protocols for managing and communicating during incidents.
Specialize in diverse cyber security domains
With the evolution of cyber security tools, specializing in diverse attack surfaces becomes imperative. Organizations should invest in developing expertise across various domains, such as cloud security, application security, and IoT, to ensure comprehensive protection.
Quantify risks for prioritized remediation
A key aspect of effective cyber security management is the ability to quantify risks in financial terms. Organizations should develop a methodology to assess the monetary impact of cyber security risks, which in turn helps prioritize remediation actions based on business impact.
Focus on reducing false positives
Reducing the rate of false positives in vulnerability detection is critical for efficient remediation. Organizations should focus on refining their detection tools and processes to improve data accuracy, which in turn fosters trust and expedites the remediation process.
Balance between specialized tools and unified solutions
In selecting cyber security tools, a balance between specialized solutions for specific needs and unified platforms that offer broader coverage is vital. While specialized tools offer depth in certain areas, a unified solution can provide a holistic view of the security posture.
Foster collaborative cyber security practices
Collaboration is key in managing cyber security risks effectively. Organizations should work closely with vendors, partners, and industry peers to share insights and best practices. This collaborative approach helps in building a more resilient and responsive cyber security ecosystem.
Watch the full session here >>
Session 10 – Defending the modern enterprise
Speakers: Dennis Van Ham, Wipro Global Head Cyber Defense & Incident Response practice
Embrace cloud transformations and multi-cloud environments
Modern enterprises are deep in their cloud transformations, a key component of modernization. Embracing multi-cloud strategies is becoming increasingly important for these organizations, demanding a comprehensive approach to security in diverse cloud environments.
Prioritize speed in modern delivery development
In the realm of modern cyber security, speed is a critical factor. Enterprises are focusing on accelerating their development processes, highlighting the need for cyber security measures that can keep pace without compromising security integrity.
Break down organizational silos
A significant aspect of modern enterprises is the dissolution of traditional organizational silos. Leveraging third-party ecosystems and service providers is crucial for enhancing cyber security while maintaining operational efficiency.
Address the find-and-fix imbalance
A persistent challenge in cyber security is the imbalance between finding vulnerabilities and fixing them efficiently. This issue often stems from governance and collaboration challenges rather than technological limitations, emphasizing the need for improved inter-departmental coordination.
The evolving role of managed services providers
Managed services providers are increasingly important in the modern enterprise landscape, offering deep insights into client IT environments. These providers play a pivotal role in ensuring that IT management is inherently secure, incorporating vulnerability management into broader IT strategies.
Overcome the frenemy dynamics in client environments
One of the biggest challenges in implementing effective cyber security strategies is breaking through the ‘frenemy’ dynamics between different departments like IT, security, and compliance. Successful programs require shared accountability and collaboration across these divisions.
Watch the full session here >>
Session 11 – Prioritize vulnerability risk with Recorded Future threat intelligence
Speakers: Chris Coburn Recorded Future principal technology alliance architect
Defining cyber threat intelligence
Cyber threat intelligence is a segmented industry sector, with different vendors approaching it uniquely. Recorded Future distinguishes itself by collecting vast amounts of data from various sources using advanced techniques like natural language processing, ontology analysis, and entity relationship mapping. This approach creates an extensive intelligence graph that provides a comprehensive view of the cyber world.
Understanding the Recorded Future intelligence graph
Recorded Future’s intelligence graph is a result of extensive data collection and analysis since 2009. It offers insights into threat actors, their methods, exploited vulnerabilities, and associated malware. This level of detailed intelligence is pivotal for organizations to understand specific threats and how to effectively counter them.
Vulnerability intelligence: Beyond CVSS scoring
Recorded Future’s vulnerability intelligence focuses on the likelihood of exploitation of vulnerabilities rather than just their potential impact (as measured by CVSS scores). This approach considers the entire lifecycle of vulnerabilities, from initial discovery to active exploitation, providing a more dynamic and actionable perspective for prioritization.
Integration of Recorded Future with Vulcan Cyber
The integration of Recorded Future’s intelligence with Vulcan Cyber allows analysts to prioritize vulnerabilities based on real-world exploitation data. This collaboration enhances the decision-making process for patching and remediation, offering context on why certain vulnerabilities are more critical than others.
Watch the full session here >>
Beyond the best practices
Taking on board cyber security advice is only one piece of the puzzle. The rich tapestry of today’s vulnerability risk environment means that security teams must rally their entire organizations to assist with the vulnerability management effort. This is often a case of aligning tools, gaining a clear picture of cyber risk, and communicating in a shared language to ensure the most pressing risk is mitigated effectively. But with so many moving parts, teams are quickly overwhelmed.
You can manage vulnerabilities and risks across all your attack surfaces at scale with the Vulcan Cyber® risk management platform. Book your demo today.