Cloud security can be a complicated matter as your enterprise expands. With more users, more configurations and more data, it’s hard to keep up and prevent unauthorized access to your protected data. One way to monitor your cloud security would be to do routine security vulnerability assessments.
Here are four steps to conducting an effective security vulnerability assessment:
- Assess your cloud provider’s security postures (all of them have homegrown security assessment capabilities – see our blogs on AWS, GCP and Azure)
- Review all security policies and protocols from your cloud providers
- Security ratings can easily automate the process and continually keep an eye on a vendor’s security posture
- Reassess your cloud services agreement depending on security ratings
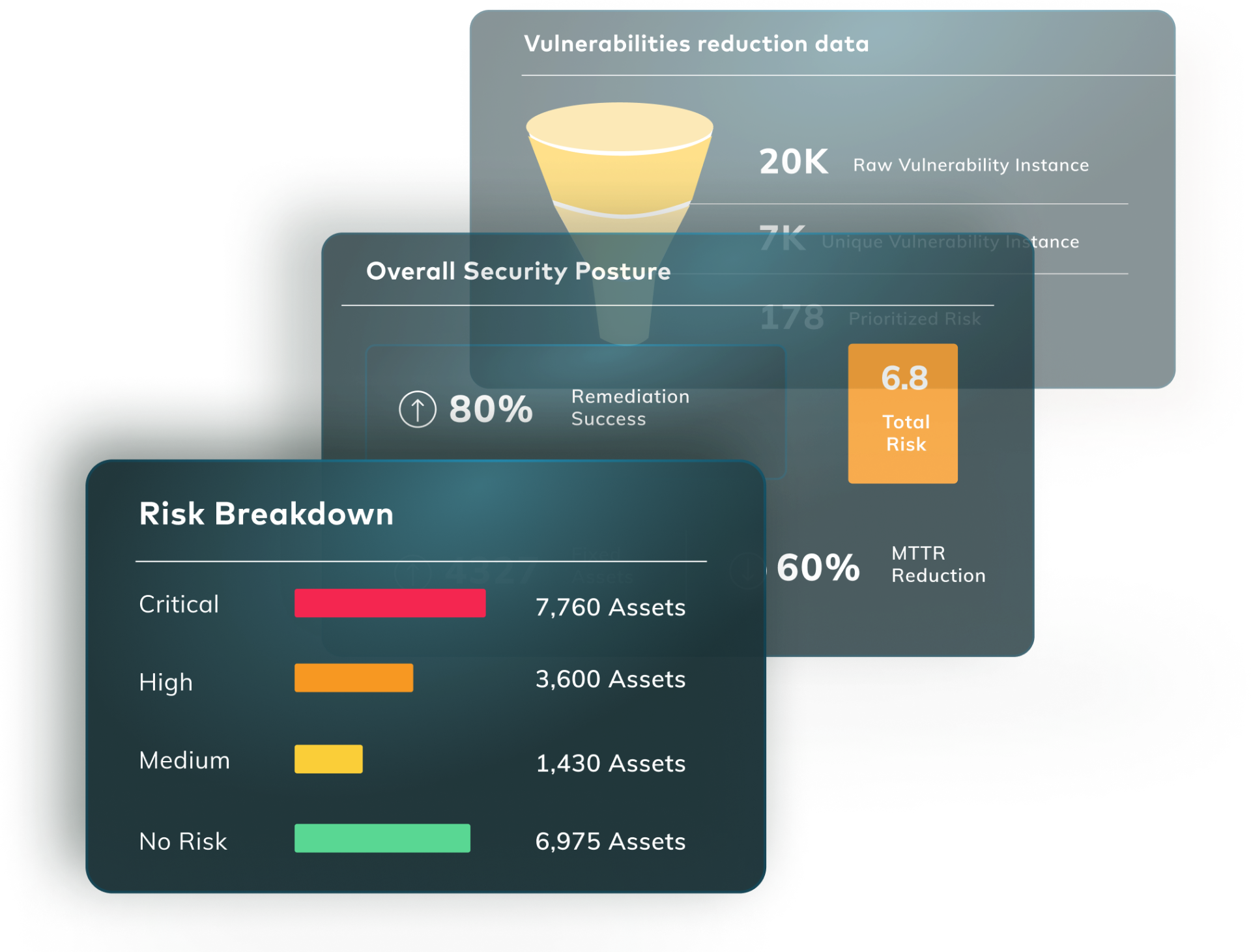
- Evaluate risk
- Perform a vulnerability scan to identify vulnerabilities, determine underlying security threats and identify suggested methods of remediation
- Prioritize vulnerabilities
- Prioritize critical vulnerabilities based on the severity of their potential impacts to your system
- Remediate effectively (in collaboration – DevOps and Dev, and stay within SLA)
- Fix the vulnerabilities to prevent any exploitation based on priority level by using the appropriate CVE
- Update software, enhance security procedures, install new security tools
After you’ve completed your vulnerability scan, Vulcan Free can help you get started on your remediation journey by prioritizing vulnerabilities according to your particular business risk. Learn how to get started today.