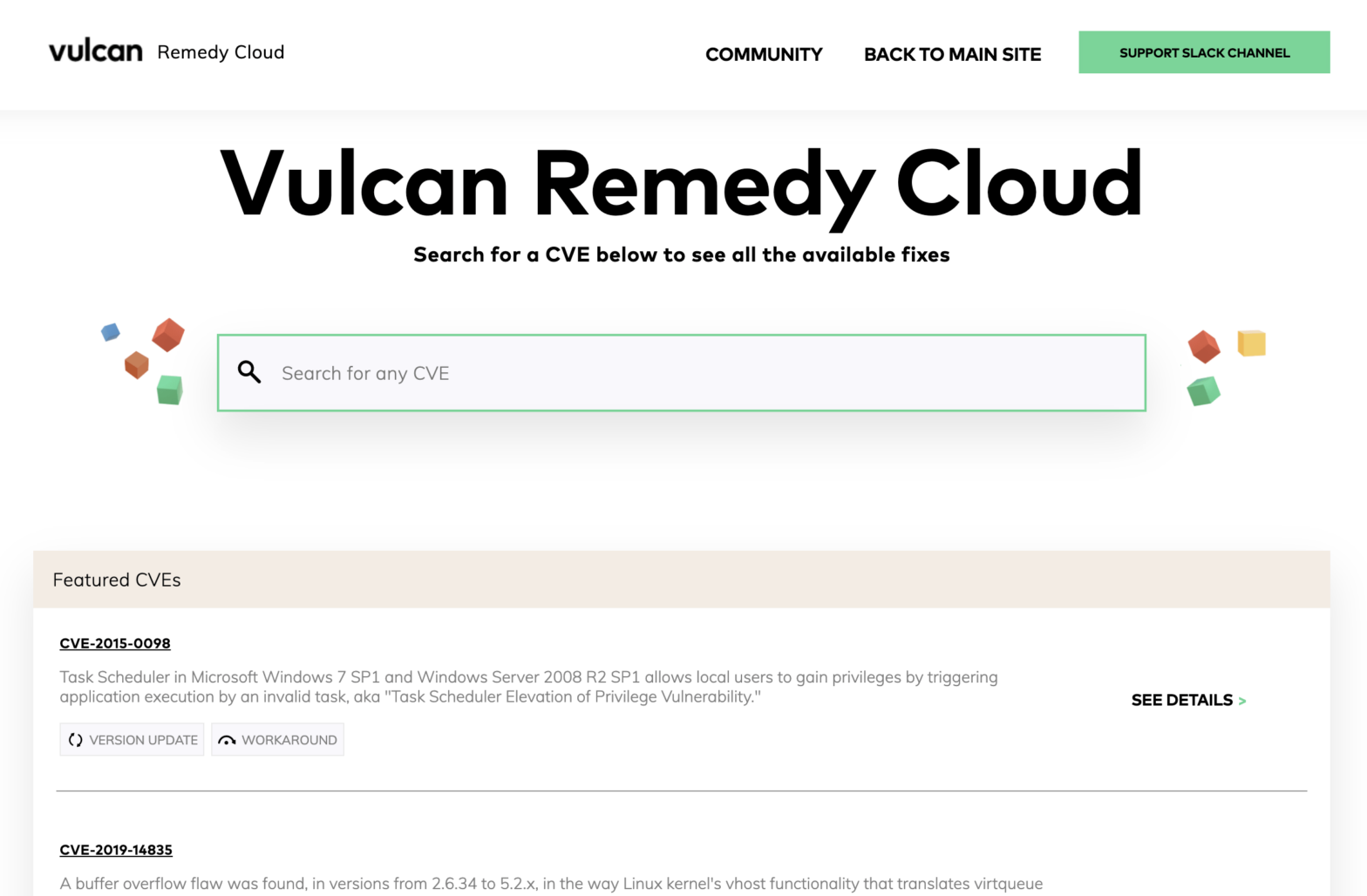
There is a well-known travel guide that is popular, in part, because it has “Don’t Panic” embossed conspicuously on the cover. In the world of cybersecurity, where new vulnerabilities and new attacks are announced on an almost daily basis, it’s a phrase we should take to heart. While we need to be aware of evolving cyber… Continue reading In large friendly letters – making sense of cyber vulnerabilities
In large friendly letters – making sense of cyber vulnerabilities