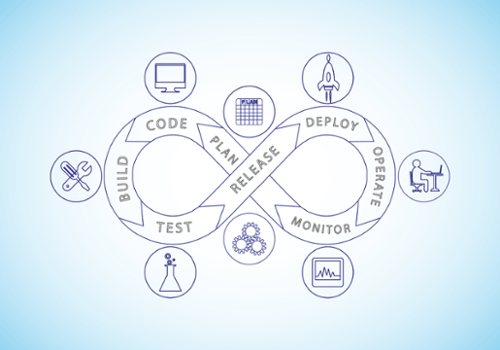
Vulnerabilities can arise in software due to existing bugs, improperly secured firewall rules, or various other reasons. If attackers succeed in exploiting these vulnerabilities, this can lead to system disruptions and serious damage to the targeted organization. KEY STAT: In 2022, 76% of organizations were targeted by a ransomware attack A thorough and efficient vulnerability… Continue reading Vulnerability management metrics in 2024: the ultimate guide
Vulnerability management metrics in 2024: the ultimate guide